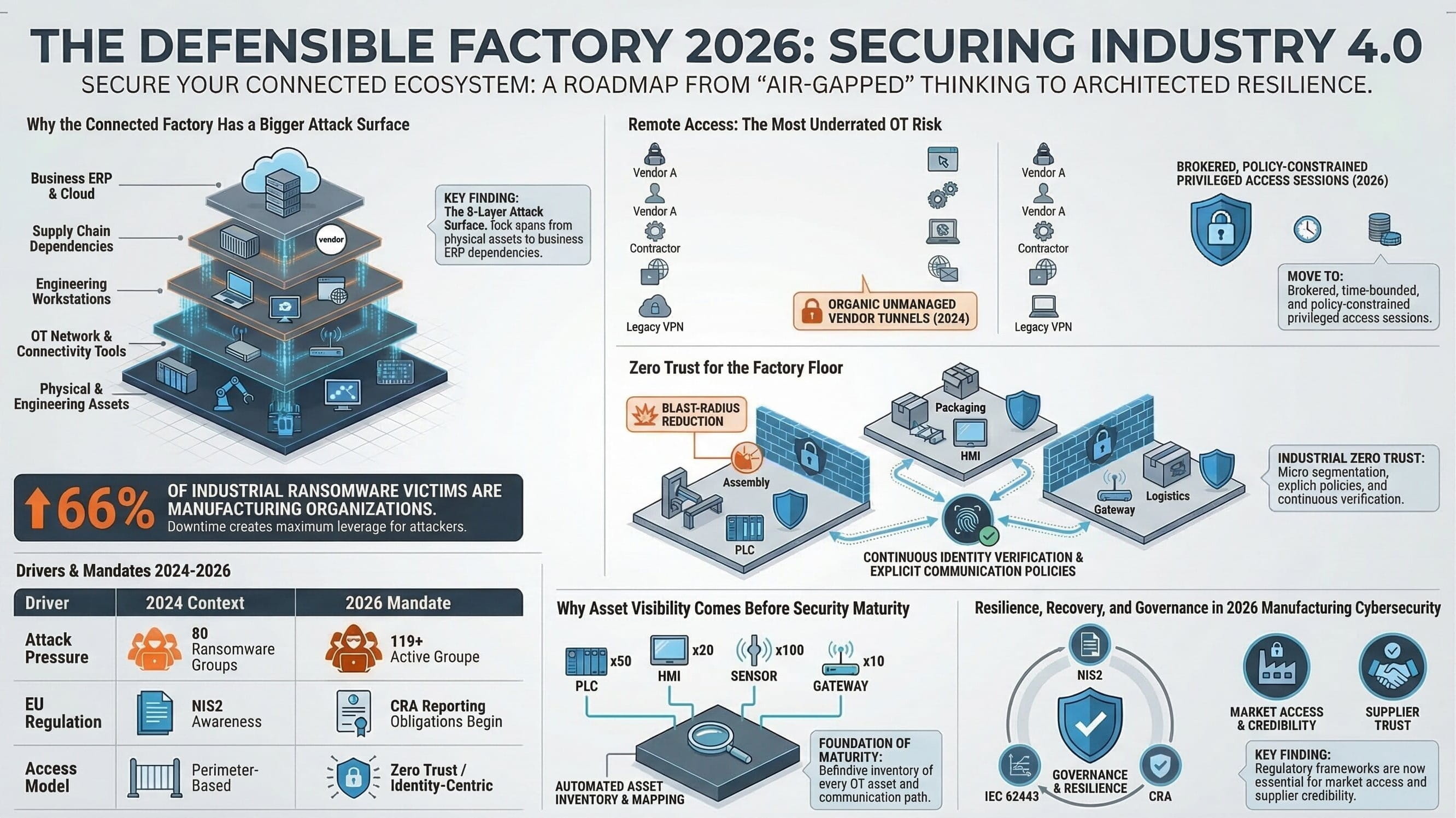
Executive summary: Industry 4.0 has transformed industrial operations from isolated control domains into highly connected decision environments. That transformation has created measurable operational value, but it has also expanded exposure across assets, engineering workstations, vendor pathways, cloud links, supplier systems, and software dependencies. The core challenge for 2026 is not merely detecting threats. It is designing a factory that can limit trust, contain blast radius, preserve safety, recover quickly, and prove governance while digital modernization continues to scale.
Why this matters now
Industry 4.0 was never only about connecting machines. It was about connecting decisions across production, quality, maintenance, supply chain execution, remote support, analytics, and enterprise planning. In practical terms, that means cyber risk in manufacturing no longer sits neatly inside the security function. It now affects uptime, product integrity, operational safety, regulatory posture, supplier trust, and executive accountability.
This is why the old “air gap” mindset has become strategically dangerous. Most modern plants are connected through historians, MES platforms, engineering laptops, remote vendor tools, IIoT gateways, wireless links, APIs into ERP, cloud dashboards, and software-defined workflows. The smart factory therefore becomes only as resilient as its least governed connection.
The strategic shift: cybersecurity in OT is no longer a “review step” after automation architecture is set. It is part of the industrial operating model itself.
The connected factory threat model: where Industry 4.0 expands risk
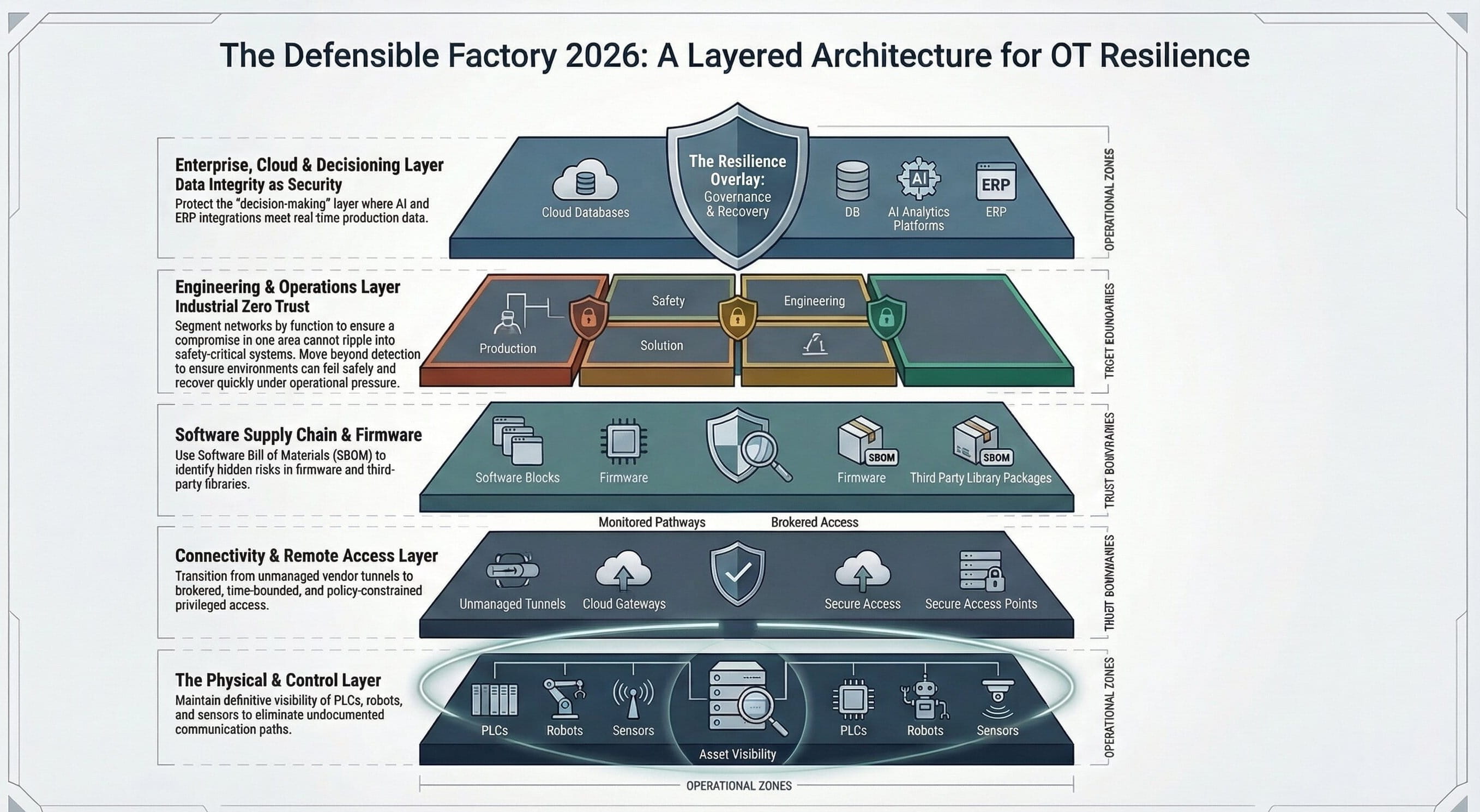
The most common mistake in industrial cybersecurity is assuming that risk lives mainly in devices. In reality, risk sits in the interaction model between assets, users, systems, software, and operational dependencies. A connected factory is exposed through five overlapping layers:
1. Asset layer
PLCs, HMIs, drives, robots, gateways, industrial PCs, sensors, and controllers form the visible OT attack surface. These are essential targets, but they are often not the first point of entry.
2. Engineering & operations layer
Engineering workstations, historian servers, maintenance laptops, batch systems, and operator interfaces often bridge enterprise compromise into production consequence.
3. Connectivity layer
VPNs, remote support tools, plant-to-cloud connectors, OPC-UA services, MQTT brokers, wireless links, and firewall exceptions turn convenience into exposure when poorly governed.
4. Software & supply chain layer
Firmware, third-party components, embedded libraries, update packages, and vendor software determine whether vulnerabilities can be identified, prioritized, and remediated responsibly.
5. Business dependency layer
ERP, supplier portals, ticketing systems, quality release workflows, identity providers, and analytics platforms directly influence resilience when manufacturing execution depends on them.
What this means
A modern cyber incident in manufacturing is rarely a clean technical event. It is often a business interruption engine that can disrupt planning, maintenance, quality, traceability, and recovery at once.
Why 2026 feels different
The urgency around industrial cybersecurity has sharpened because three curves are converging at once: attack pressure, regulatory pressure, and architectural dependence on software. Manufacturing remains attractive to attackers because downtime is expensive and recovery is hard. At the same time, European expectations around cyber governance, product security, and incident discipline are becoming more formal. Meanwhile, plants are relying more heavily on remote visibility, cloud workflows, and AI-assisted systems—eliminating the old fiction that cybersecurity can remain a narrow network-hardening exercise.
In 2026, the real question is no longer whether a plant has antivirus, firewalls, or a SOC connection. The question is whether the industrial architecture itself was designed to fail safely, authenticate rigorously, isolate intelligently, and restore under pressure.
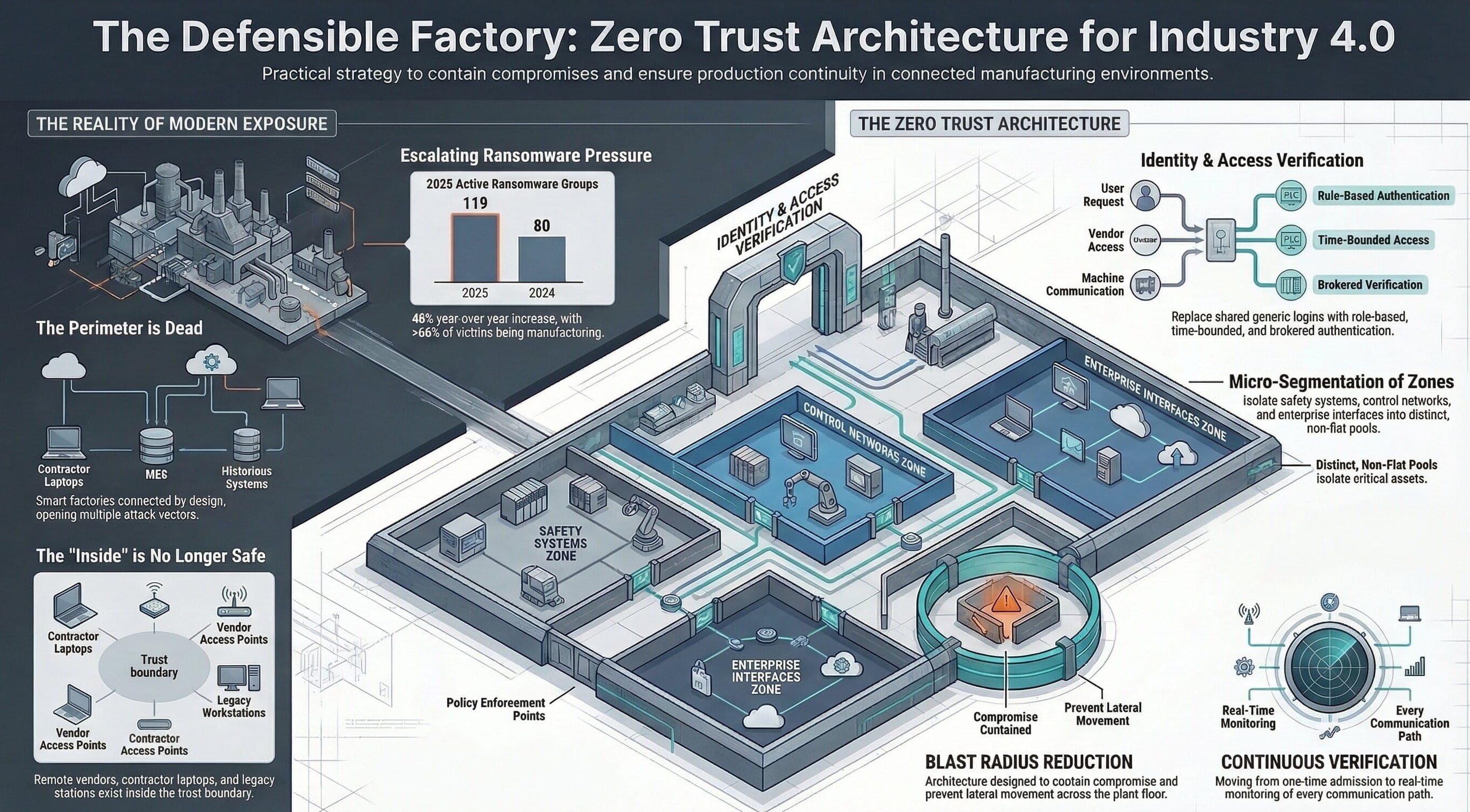
Zero Trust for the factory floor: useful when treated as discipline, not slogan
Zero Trust is frequently misunderstood in OT. It is not about importing an enterprise security template and applying it blindly to production. It is about one discipline applied consistently: never assume trust simply because a user, device, or system is already inside the perimeter.
What it means in practice
- Strong identity assurance for people, services, and remote vendors.
- Explicit communication policies instead of all-to-all connectivity.
- Segmentation by function and operational consequence.
- Awareness of user role, device condition, and session context.
- Continuous verification, not one-time admission.
What it is really doing
In manufacturing, Zero Trust is best understood as a blast-radius reduction model. It slows lateral movement, reduces standing privilege, improves monitoring quality, and limits operational damage when compromise occurs.
Watch: architecting the defensible factory
For teams that prefer a visual walkthrough, use the video briefing below as a companion asset within the blog package.
Listen: securing the connected factory floor
For leadership teams, plant heads, or architects reviewing this topic on the move, the audio version provides a lightweight executive listening path.
The most underrated weakness in smart factories: remote access
Modern manufacturing depends on remote support. Vendors need access to troubleshoot equipment. Engineers need visibility across sites. Specialists need to diagnose alarms, logs, and performance deviations without travel delays. The problem is not remote access itself. The problem is unmanaged remote access.
Many plants accumulate remote pathways over time: one VPN for a vendor, one firewall exception during an outage, one shared admin credential, one contractor laptop, one remote desktop hop nobody decommissions. The result is an environment where access paths exist, but ownership, logging, approvals, and session control do not.
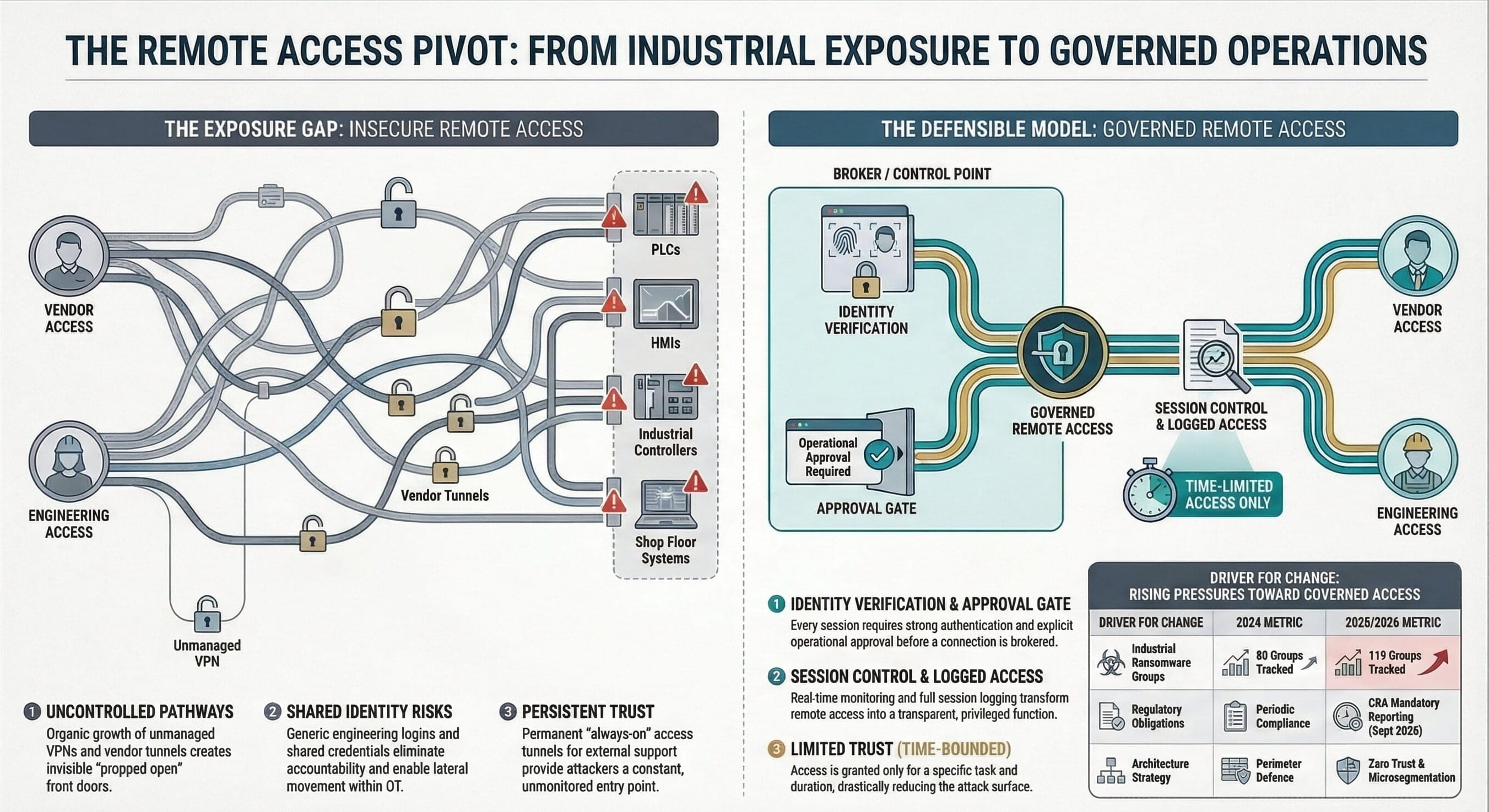
| Weak pattern | Operational consequence | Defensible pattern |
|---|---|---|
| Persistent vendor tunnels | Standing exposure with unclear ownership | Brokered sessions with approval, MFA, and time limits |
| Shared engineering credentials | No traceability during change or incident response | Named identity, role-based access, auditable session logs |
| Flat remote reach into OT | Fast lateral movement after compromise | Segmented conduits and explicit destination restrictions |
| Untracked remote tools | Hidden attack paths and governance blind spots | Central inventory, owner assignment, review cadence |
Compliance is no longer a side conversation
Many manufacturers still ask whether a specific law technically applies to them. That is no longer the only relevant question. A better one is: what will customers, regulators, insurers, and strategic partners expect us to prove?
Cyber governance now shapes commercial credibility. NIS2 raises expectations around risk management, governance, and incident discipline. The Cyber Resilience Act pushes product security further upstream. IEC 62443 remains an anchor framework for industrial automation and control system security. Software transparency and SBOM-aware procurement increasingly determine whether organizations can respond to vulnerabilities with confidence rather than guesswork.
NIS2
Raises the maturity floor around accountability, cyber risk management, and incident readiness across critical sectors.
Cyber Resilience Act
Moves security expectations into the product lifecycle, vulnerability handling process, and evidence-backed development discipline.
IEC 62443 & SBOMs
Provide practical structure for secure industrial architecture, supplier scrutiny, and software dependency visibility.
AI in industrial cybersecurity: powerful accelerator, poor substitute
AI can improve anomaly detection, correlate suspicious behavior, reduce alert fatigue, and help smaller teams investigate larger telemetry volumes. Those benefits are real. But AI does not erase fundamentals. If you lack asset inventory, segmentation, identity control, or tested recovery plans, AI will not compensate for those structural weaknesses.
The best teams use AI as an accelerator layered onto disciplined controls. The correct sequence remains clear: build visibility, establish architecture, control identities and remote access, harden based on operational consequence, instrument detection and response, and then use AI to improve speed and accuracy across that foundation.
Bottom line: the advantage in 2026 does not go to the team that says “AI” the loudest. It goes to the team that integrates AI into well-governed operational controls.
The forgotten foundation: asset inventory and architecture visibility
The biggest barrier to industrial resilience is often not the absence of a tool. It is the absence of architectural truth. Many plants still rely on fragmented knowledge: aging network diagrams, tribal memory, spreadsheet lists of PLCs, undocumented firewall rules, and maintenance laptops that are operationally critical but not centrally governed.
A serious industrial cybersecurity program begins by answering a deceptively basic set of questions: What assets exist? Which are safety-critical? Which bridge IT and OT? Which communicate externally? Which run unsupported platforms? Which vendor pathways exist? Which applications hold privileged access? Which recovery dependencies are undocumented?
Until those questions are answered, every downstream control discussion remains partial.
ROI and risk logic: why the defensible factory outperforms the merely connected one
Security investment in industrial environments is often framed as a compliance cost. That framing is too narrow. A defensible architecture produces measurable operational value by reducing downtime exposure, limiting incident spread, strengthening supplier trust, improving audit readiness, and preserving confidence in operational data.
| Capability | Risk reduced | Operational value created |
|---|---|---|
| OT segmentation | Lateral movement and cross-zone blast radius | Faster containment, cleaner recovery boundaries |
| Privileged remote access governance | Unauthorized or weakly controlled vendor sessions | Auditability, traceability, lower outage probability |
| Asset inventory and architecture visibility | Blind spots during patching, response, and recovery | Better prioritization, better executive decisions |
| SBOM-aware procurement | Unknown software dependencies and slow vulnerability treatment | Higher supplier confidence and faster remediation planning |
| Tested recovery plans | Extended production disruption during crisis | Shorter restoration timelines and safer restart decisions |
Implementation roadmap: how manufacturers should respond
The gap between immature and mature industrial cybersecurity programs is now obvious. Immature programs chase tools. Mature programs redesign trust, evidence, and recoverability. The most practical way forward is a phased architecture-led program:
Phase 1 — Establish architectural truth
Create a definitive OT asset inventory, map trust boundaries, identify external pathways, document engineering dependencies, and classify critical production systems by operational consequence.
Phase 2 — Reduce standing exposure
Clean up remote access, enforce stronger identity controls, eliminate shared credentials, close unmanaged tunnels, and constrain communications to approved conduits.
Phase 3 — Segment by function and consequence
Separate safety, control, historian, engineering, remote support, and enterprise-facing services into governed zones that slow lateral movement and simplify containment.
Phase 4 — Strengthen software and supplier governance
Introduce SBOM-aware procurement, vulnerability handling discipline, secure update pathways, and evidence-backed supplier review processes.
Phase 5 — Test resilience under pressure
Exercise recovery plans, validate backup restoration, rehearse site isolation decisions, and verify that operational leaders can make safe restart decisions under disruption.
Phase 6 — Add AI where the foundation is ready
Use AI to improve detection quality, investigation speed, and signal prioritization only after architecture, identity, segmentation, and recovery controls are trustworthy.
The board-level questions that actually matter
The wrong executive question is “Are we protected?” No honest technical leader can answer that with certainty. The right questions are more rigorous:
- Can we identify our critical OT assets and dependencies?
- Can we prove who has access to them and under what controls?
- Can we contain compromise if one site or supplier pathway is breached?
- Can we restore safely under operational pressure?
- Can we demonstrate governance to customers and regulators?
- Can we keep modernizing without increasing uncontrolled risk?
Those questions reflect the real standard for Industry 4.0 resilience in 2026: not perfect protection, but the ability to absorb disruption without operational collapse.
Final takeaway: the smart factory must also be a defensible factory
The most advanced factory is not the one with the most dashboards, the most cloud connectors, or the most AI labels in a vendor presentation. It is the one built on disciplined architecture. It knows its assets. It limits trust. It governs remote access. It segments intelligently. It understands software dependencies. It plans recovery honestly. And it aligns operations, engineering, IT, and cybersecurity around one shared resilience model.
Manufacturers that understand this will do more than reduce cyber risk. They will digitize faster, withstand customer scrutiny more confidently, operate with less hidden fragility, and scale connected operations with stronger control over consequence.
Enhanced Full Blog Text — Board-Ready Report Format
Cybersecurity in the Age of Industry 4.0: Securing the Connected Factory in 2026
Executive summary: Industry 4.0 has changed the cybersecurity debate in manufacturing from a narrow technical concern into a core business resilience question. The modern factory is not merely connected; it is decision-linked across operations, quality, ERP, suppliers, cloud services, remote support channels, and software-defined workflows. That creates major upside in speed, efficiency, and visibility. It also creates a larger and more complex attack surface. In 2026, the manufacturers that will outperform are not simply the most digitized—they are the ones that can prove that their connected operations are architected to remain safe, governable, and recoverable under cyber pressure.
Industry 4.0 was never just about connecting machines
Industry 4.0 was never just about connecting machines. It was about connecting decisions.
That distinction matters more in 2026 than it did even two years ago. The modern factory is no longer a collection of isolated PLCs, SCADA screens, historian databases, and maintenance routines stitched together with tribal knowledge. It is now an operating environment where production assets, quality systems, ERP transactions, remote access channels, cloud workloads, third-party support connections, AI-assisted analytics, and software-defined workflows interact in real time. That has created enormous upside for manufacturers. It has also created a brutally larger attack surface.
For years, industrial cybersecurity was framed as a side discipline: something the security team reviewed after automation decisions had already been made. That model is dead. In a connected plant, cybersecurity is no longer an IT governance topic. It is a production continuity issue, a safety issue, a supplier trust issue, and increasingly a board-level risk issue.
This is why the old air gap mindset has become dangerous nostalgia. Most plants are not isolated. They are connected through historians, MES platforms, vendor remote support tools, IIoT gateways, cloud dashboards, API links into ERP, VPN concentrators, engineering workstations, and sometimes badly governed edge devices nobody remembers approving. The result is a hard truth many firms still avoid: the smart factory is only as resilient as its least governed connection.
The good news is that industrial cybersecurity in 2026 is far more mature than the old checklist era. The best organizations are no longer chasing security as a compliance theater exercise. They are engineering it into architecture, access control, software procurement, remote operations, recovery planning, and even analytics design. They are moving from “Can we detect an attack?” to “Can this environment continue to operate safely, contain the blast radius, recover quickly, and prove governance to customers and regulators?”
That is the real cybersecurity conversation in Industry 4.0 now.
The new threat model: why Industry 4.0 changes the stakes
Traditional industrial environments had weaknesses, but they also had friction. Connectivity was limited. External access was constrained. Machine data did not flow freely into enterprise or cloud systems. Operational decisions depended heavily on human intervention. In that world, cybersecurity failures could still be catastrophic, but the pathways were fewer.
Industry 4.0 changes that by design.
The same capabilities that deliver value also expand risk. Remote monitoring creates external pathways. Predictive maintenance requires data collection at scale. Cross-site benchmarking requires normalization layers and integration into centralized platforms. AI-based anomaly detection needs high-quality, persistent access to machine and process data. Supplier collaboration introduces identity, API, and data-sharing dependencies. Every one of those steps improves operations. Every one also creates security implications.
The mistake many companies still make is assuming the risk resides mainly in the “devices.” It does not. The risk sits in the interaction model.
A connected factory is exposed through five overlapping layers.
First, there is the asset layer: PLCs, HMIs, sensors, industrial PCs, robots, gateways, drives, and controllers. These are the obvious targets, but they are not always the first entry point.
Second, there is the engineering and operations layer: engineering workstations, maintenance laptops, historian servers, batch systems, and operator interfaces. These systems often run standard operating systems, inherit weak credential practices, and become the bridge between enterprise compromise and production impact.
Third, there is the connectivity layer: remote support tools, VPNs, firewalls, wireless links, serial-to-Ethernet converters, OPC-UA servers, MQTT brokers, API gateways, and plant-to-cloud connectors. This is where convenience quietly becomes exposure.
Fourth, there is the software and supply chain layer: firmware, third-party libraries, update packages, embedded components, vendor software, and device management systems. This is where software transparency, supplier discipline, and lifecycle security become critical.
Fifth, there is the business dependency layer: ERP integrations, supplier portals, cloud analytics, ticketing systems, maintenance workflows, and identity providers. These systems may not “look OT,” but they directly affect operational resilience when a plant relies on them for scheduling, quality release, material movement, or coordinated response.
That is the threat model most blog posts still miss. Industry 4.0 risk is not just about a hacker “taking over a machine.” It is about how a compromise in one digital dependency can ripple into production scheduling, maintenance execution, quality decision-making, safety procedures, or recovery timelines.
In other words: a modern cyber incident in manufacturing is rarely a clean technical event. It is a business interruption engine.
Why 2026 feels different
Industrial leaders have been hearing warnings about cybersecurity for years, so why does the topic feel sharper in 2026?
Because three separate curves are converging.
The first is attack pressure. Manufacturing continues to attract attackers because downtime is expensive, recovery is complicated, and the tolerance for disruption is low. Attackers understand that a plant shutdown, shipment delay, recipe loss, quality compromise, or supplier disruption creates leverage.
The second is regulatory pressure. In Europe, cybersecurity expectations are becoming more formal. This is not the year to “start thinking about this later.” It is the year many organizations must operationalize supplier scrutiny, product security expectations, vulnerability handling discipline, and evidence-backed governance.
The third is architectural dependence on software. Plants are doing more with remote visibility, cloud orchestration, AI-based detection, and IT/OT convergence. That increases business value, but it also removes the old fiction that cybersecurity can remain a narrow network-hardening exercise. It now has to encompass identities, configurations, segmentation, software provenance, remote access discipline, and recoverability.
That is why the conversation has matured. In 2026, cybersecurity is no longer about whether a plant has antivirus and a firewall. It is about whether the industrial architecture itself was designed to fail safely, authenticate rigorously, isolate intelligently, and recover under pressure.
Zero Trust for the factory floor: useful, but often misunderstood
Zero Trust is one of the most abused terms in cybersecurity. In industrial environments, it is either oversimplified into marketing fluff or rejected as if it were an IT-only concept that has no place near production systems. Both reactions are lazy.
The value of Zero Trust in manufacturing is not in copying enterprise templates. It is in applying one discipline consistently: never assume trust just because something is inside the perimeter.
That matters in plants because “inside” no longer means “safe.” Remote vendors are inside. Contractor laptops are inside. Legacy engineering stations are inside. Flat networks are inside. Shared admin credentials are inside. Unpatched HMIs are inside. Misconfigured jump hosts are inside. The idea that internal network position equals legitimacy is precisely what enables lateral movement.
In practice, a usable Zero Trust approach for Industry 4.0 means several things:
It means strong identity assurance for people, systems, and services. No more generic engineering logins shared across shifts. No more permanent vendor access tunnels just because “support might be needed.”
It means explicit communication policy. A machine, workstation, or gateway should only talk to the systems it actually needs to talk to. Not everything to everything.
It means segmentation based on function and consequence. Safety systems, control networks, historian services, remote support channels, and enterprise interfaces should not exist in one undifferentiated trust pool.
It means device and session awareness. Access decisions should account for user role, device condition, session context, and operational purpose.
It means continuous verification rather than one-time admission.
The point is not to make the plant unusable. The point is to make compromise harder, movement slower, detection faster, and damage smaller.
That is the real industrial interpretation of Zero Trust. Not a slogan. A blast-radius reduction strategy.
The most underrated weakness in smart factories: remote access
Ask enough plant teams where they feel exposed and one answer keeps resurfacing: remote access.
Not because remote access is inherently reckless. It is not. Modern manufacturing depends on it. Vendors need to support equipment. Engineers need to troubleshoot across sites. Specialists need visibility into alarms, logs, and configurations. Multi-site operations require remote collaboration. The problem is not remote access itself. The problem is unmanaged remote access.
In too many environments, remote support grew organically. One VPN here, one vendor tunnel there, one firewall exception nobody retired, one shared local admin credential, one laptop approved in a hurry during an outage. Over time, the plant accumulates access paths that no one fully owns.
That is a terrible security posture.
Remote access in 2026 should be treated as a privileged operational function, not a convenience feature. Every remote session should be brokered, authenticated, logged, time-bounded, and policy-constrained. There should be approved pathways, session visibility, and clear ownership over who can connect, from where, to what, for how long, and under whose authorization.
This is where many manufacturers still lag. They spend on detection tools while leaving the front door propped open through unmanaged vendor access. That is backward. Secure remote connectivity is not secondary control hygiene. It is one of the main control points in a connected factory.
Compliance is no longer a side conversation
A lot of manufacturers still ask the wrong question about compliance: “Do we legally fall under this?”
The better question is: “What will customers, regulators, insurers, and partners expect us to prove?”
Cybersecurity governance now influences market access, supplier credibility, contract conversations, customer due diligence, and insurance posture. Compliance is increasingly a commercial trust layer.
The point is not that every mid-market manufacturer must become a regulatory scholar. The point is that cybersecurity governance now influences market access, supplier credibility, contract conversations, customer due diligence, and insurance posture. The firms that still treat it as paperwork are going to discover, too late, that the market treats it as operational credibility.
AI in industrial cybersecurity: where it helps, where it lies
AI is now everywhere in security marketing, which is exactly why it needs to be discussed carefully.
Yes, AI can materially improve detection and triage in complex environments. It can correlate anomalies across asset behavior, login patterns, network communications, process deviations, and user activity. It can speed up investigation. It can prioritize alerts. It can help smaller teams handle larger volumes of telemetry. These are real advantages.
But AI does not erase the fundamentals.
If you have no trustworthy asset inventory, AI cannot protect what you cannot identify. If your network is flat, AI may tell you that compromise is spreading, but architecture already failed you. If remote access is unmanaged, AI will not compensate for weak identity control. If backups are untested, AI will not restore operations. If engineering workstations are treated like generic office PCs, AI will not magically understand their production-critical role.
This is where the best industrial teams are getting smarter. They use AI as an accelerator, not a substitute. They know the real sequence is:
1. build asset visibility,
2. establish architecture and segmentation,
3. control identities and remote access,
4. harden and patch according to operational reality,
5. instrument detection and response,
6. use AI to increase speed and accuracy across that foundation.
Anything else is theater.
There is a second reason to stay grounded: attackers use AI too. They use it to refine phishing, accelerate reconnaissance, personalize lures, and streamline exploitation at scale. So the 2026 security advantage does not belong to whoever says “AI” the loudest. It belongs to whoever integrates AI into disciplined operational controls.
The forgotten foundation: asset inventory and architecture visibility
If there is one problem that keeps sabotaging industrial cybersecurity programs, it is not a missing tool. It is incomplete visibility.
You cannot secure what you do not know exists.
Yet in many plants, asset knowledge still lives in fragments: an old network diagram, a PLC list from engineering, firewall rules known only to one admin, maintenance laptops not tracked centrally, and vendor equipment with undocumented communication paths. That is not resilience. That is dependence on memory.
A serious 2026 industrial cybersecurity program starts with architectural truth:
What assets exist?
Which ones are safety-critical?
Which ones are production-critical?
Which ones communicate externally?
Which ones bridge IT and OT?
Which ones depend on unsupported operating systems?
Which vendor pathways exist?
Which applications have privileged access?
Which sites are most exposed?
Which recovery dependencies are undocumented?
Until those questions are answered, everything else is partial.
This is also why board-level cybersecurity discussions often go nowhere. Leaders ask whether the company is secure. The real answer is often: “We do not yet have a definitive view of the environment we are trying to secure.”
That is not a tool gap. That is a management gap.
Ransomware is still the loudest signal, but it is not the whole story
Ransomware gets attention because it is visible. Plants stop. Screens go dark. Orders slip. Media notices. Executives panic.
But focusing only on ransomware is a mistake.
Industrial cybersecurity risk also includes extortion without encryption, supplier compromise, credential theft, unsafe remote manipulation, recipe tampering, integrity attacks against quality systems, data exfiltration involving process IP, and targeted disruption through engineering environments. Modern attackers do not always need to “take over the plant” to create serious harm. Sometimes they only need to corrupt trust in data, delay production decisions, or compromise the systems that coordinate operations.
That matters because Industry 4.0 runs on trusted information flows. If machine data cannot be trusted, predictive models degrade. If quality records are suspect, traceability collapses. If maintenance data is incomplete, planned downtime becomes guesswork. If supplier interfaces are exposed, third-party risk jumps. If historian integrity is compromised, root-cause analysis becomes contaminated.
This is why cyber resilience must be treated as both a security discipline and a data integrity discipline.
The connected factory is not just vulnerable when machines stop. It is vulnerable when decision systems quietly become unreliable.
What best practice looks like in 2026
By now, the gap between mature and immature industrial cybersecurity programs is obvious.
Immature programs chase tools.
Mature programs design control.
Immature programs ask whether a specific product can “do Zero Trust.” Mature programs redesign trust boundaries.
Immature programs treat OT as too fragile to touch. Mature programs accept that poorly governed OT is already fragile.
Immature programs wait for audits. Mature programs create evidence continuously.
So what does strong practice actually look like now?
It looks like security architecture aligned with operational reality.
It looks like segmented networks, controlled conduits, and reduced lateral movement opportunity.
It looks like privileged remote access with strong authentication, approvals, monitoring, and time limits.
It looks like accurate OT asset inventory and architecture visibility.
It looks like patching and vulnerability treatment based on operational consequence, not generic IT service windows.
It looks like software transparency, supplier scrutiny, and SBOM-aware procurement.
It looks like backup and recovery designs that assume an industrial incident will happen and that restoration must be tested, not merely documented.
It looks like security teams and operations teams working from a shared risk model instead of acting like rival tribes.
And critically, it looks like leadership understanding that cybersecurity is not the tax paid for digitization. It is the condition for digitization to scale safely.
The board-level question every manufacturer should be asking
The wrong board question is:
“Are we protected?”
No honest technical leader can answer that with a yes.
The right questions are harder:
Can we identify our critical OT assets and dependencies?
Can we prove who has access to them?
Can we contain compromise if one site or supplier pathway is breached?
Can we restore safely under operational pressure?
Can we demonstrate governance to customers and regulators?
Can we continue digital modernization without increasing uncontrolled risk?
That is the level of seriousness Industry 4.0 cybersecurity now demands.
Because the real issue is not whether cyber risk exists. It does. The issue is whether the organization is architected to absorb it without operational collapse.
Final thought: the smart factory must also be a defensible factory
Industry 4.0 promised speed, visibility, automation, and data-driven decision-making. It delivered all of those. But it also exposed a brutal truth: the more intelligent the factory becomes, the more dangerous unmanaged trust becomes.
That is the central cybersecurity lesson of 2026.
The defensible factory is not the one with the most dashboards, the most AI labels, or the thickest stack of security products. It is the one built on disciplined architecture. It knows its assets. It limits trust. It governs remote access. It segments intelligently. It understands software dependencies. It plans recovery honestly. It aligns operations, engineering, and security instead of pretending those domains can stay separate.
That is what resilience looks like now.
And that is why cybersecurity is no longer a support function in Industry 4.0. It is part of the operating model itself.
The manufacturers that understand this will not just avoid disaster. They will digitize faster, partner more credibly, satisfy customer scrutiny more confidently, and scale connected operations with less hidden fragility.
Everyone else will keep mistaking connectivity for maturity.
And in 2026, that is an expensive mistake.


Arjun updated on 06 Mar 2026, 08:12AM
This is one of the better explanations I’ve seen of why OT cybersecurity is really an operating-model issue now. The point about unmanaged remote access being the quietest but most dangerous exposure matches what we see across multi-site plants.Lena updated on 06 Mar 2026, 10:01AM
Agreed. We spent two years improving threat detection, but our biggest control gap was still vendor connectivity. Once we added approvals, time-bounded sessions, and proper logging, the entire risk discussion changed.Tobias updated on 06 Mar 2026, 01:44PM
The distinction between “connected” and “defensible” is excellent. A lot of leadership teams still assume digital maturity and security maturity move together. They don’t.Meera updated on 07 Mar 2026, 09:18AM
The section on architecture visibility is especially important. In our case, the biggest blocker was not tooling but the fact that no single team owned the authoritative OT asset map across plants, gateways, engineering laptops, and support paths.Daniel updated on 07 Mar 2026, 11:26AM
That’s exactly the governance gap many firms underestimate. Until ownership is explicit, every risk conversation stays theoretical.Felix updated on 07 Mar 2026, 03:52PM
Useful treatment of Zero Trust. Too many articles either oversell it as a product or dismiss it as irrelevant for manufacturing. Framing it as blast-radius reduction is much more practical.Kavya updated on 08 Mar 2026, 08:37AM
The compliance angle is timely. Customers increasingly ask us to prove process discipline, not just say that we take cybersecurity seriously. Evidence-backed governance is becoming part of commercial credibility.Jonas updated on 08 Mar 2026, 12:15PM
Yes, and procurement teams are now asking sharper questions on supplier access, patch handling, and software transparency. Security posture is showing up earlier in the deal cycle.Nikhil updated on 09 Mar 2026, 09:03AM
The AI section is refreshingly grounded. AI helps, but it cannot compensate for flat networks, weak identity controls, or poor recovery planning. That sequence you outlined should be pinned in every OT program office.Greta updated on 10 Mar 2026, 02:21PM
What stood out for me was the focus on data integrity, not just downtime. In smart factories, corrupted trust in historian data, quality records, or process context can be just as disruptive as a full shutdown.Omar updated on 11 Mar 2026, 10:46AM
This should be required reading for boards reviewing smart factory investment plans. The real question is not whether a plant is digitizing, but whether it can absorb cyber disruption without operational collapse.Hannah updated on 11 Mar 2026, 01:08PM
Exactly. The strongest takeaway here is that cybersecurity is no longer the tax paid for modernization. It is the condition that makes modernization scalable.